SIM Card Forensics — Inside Out
Recover Messages & Information from Mobile Phone SIM Cards
SIM Card Forensics — Cracking SIM Card Evidence
The involvement of a wide range of hardware / software applications is made to service SIM card forensics for restoration and analysis of its data repository. Both; the volatile as well as non-volatile data in a SIM card is of primary concern, hence, is preserved with much care. Thus, write blocker integrated workstations are used while performing SIM card data forensics.
Subscriber Identity Module — Understanding SIM
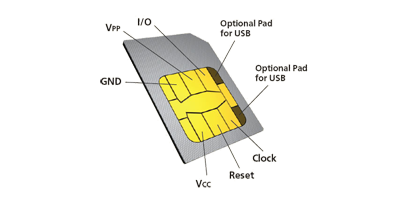
SIM – Subscriber Identity Modules are the tiny looking microcontroller smart card modules used in mobile devices. These capably store information as critical as call logs, exchanged text messages, contact details, operator details, device details, etc. If you think that’s a lot for a tiny smartcard to do, then you must not be aware of the fact that a SIM has its own set of OS, EEPROM, Processor, ROM, and RAM, etc.
Nevertheless, amongst brands like; Microsoft Hyper-V, Virtual Box, etc.; VMware tops the list as the most used tool for virtualization of computing devices and resources.
Storage File System of SIM Cards
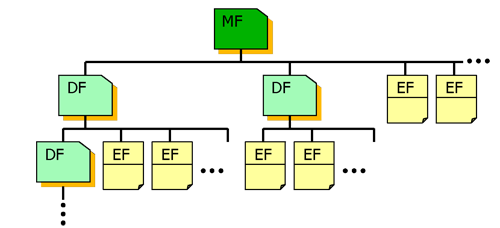
For the storage and processing of each type of data, SIM card circuits consist of separate sections. MF, DF, and EF are the Master, Dedicated, and Elementary File systems in that order. MF being the root of all file systems, has DF and EF as its subordinate directories. These file system hold on to various structured data as the sequence of either data bytes, regularly used records of fixed size, or limited size of records, respectively.
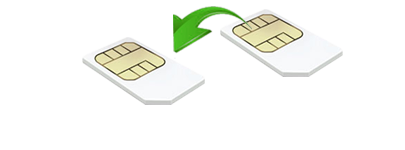
SIM Card Imaging — Enhanced Forensic Analysis
We use an imaging technique for the complete SIM card data forensics and recovery of SIM Card contents. SIM Card imaging is a process that creates an exact replica image of your SIM Card content to be processed during SIM card forensics purposes. The technique is offered to keep original evidence intact while the replica image is being used for repeated analysis.
SIM Retrieval — Recalling Deleted Entries & Content

The name and size of this module may be small but the purpose isn’t. These smart cards are designed with their own Java Card and voltage supply for programming or omitting non-volatile storage. Through our services, we offer you with the choice of getting back these deleted entries from a SIM card including; text messages, call logs, and contact details of a mobile device, etc.