Technology | 4 Minutes Reading
iCloud Forensics to Acquire Digital Evidence from iCloud in a Forensically Sound Manner

In today’s digital world, cloud storage services have become integral parts of our lives. One such popular cloud storage platform is iCloud provided by Apple. It offers a convenient way to store and sync data across devices. However, with convenience comes the risk of a security breach. Even the iCloud platform couldn’t stay immune to such security breaches. That’s when iCloud forensics comes into the picture. Let’s uncover what it means, the challenges, and its critical role in the modern investigation processes.
Understanding iCloud
Before discussing what is iCloud forensics, it’s important to understand what is iCloud. It is Apple’s cloud-based storage service. It can seamlessly sync and share data across Apple devices such as iPhones, iPads, etc. Since it can be synced across multiple devices, it raises concerns related to data privacy and security.
Thus, when the iCloud is compromised then forensic investigation of the same is required to uncover the crucial evidence.
What is iCloud Forensics?
It is a systematic process that forensic professionals follow to extract data from iCloud and analyze the same using a specialized tool such as MailXaminer. The extracted data involves contacts, messages, call logs, photos, and application data.
Investigating iCloud data may seem simple, but, there are some challenges faced by the investigators.
Challenges in iCloud Forensics
1. End-to-End Encryption
Apple emphasizes end-to-end encryption for user data including iMessage conversations and FaceTime calls. This poses a challenge for investigators to access and interpret the encrypted data for the investigation.
2. Limited Third-Party Tools
Unlike other cloud storage services, Apple tightly puts restrictions on the access of iCloud data. Due to this forensic professionals rely on professional tools for doing the investigation.
3. Data Fragmentation
Fragmentation results from the frequent distribution of iCloud data among multiple services. The forensic procedure is made more difficult by the need to carefully reconstruct data from several sources to piece together a complete picture.
4. Legal and Ethical Concerns
The legal environment of iCloud forensics is always changing. It’s difficult to strike a balance between user privacy rights and the requirement for justice. To ensure that their acts are compliant with the law, forensic specialists are required to abide by legislative frameworks and ethical norms. Hence, poses a challenge while doing the investigation.
Also, Read about Apple Mail Forensics.
Role of Forensic Analysis of iCloud in an Investigation
iCloud forensics plays an important role in various scenarios. Such as
- Criminal Investigation – Law enforcement agencies get a lot of help from performing the forensic analysis of iCloud. They get valuable insights related to the activities and communications of suspects.
- Uncovering Cybersecurity Incidents – If a security incident, such as a data breach or unauthorized access, occurs then iCloud forensics helps professionals understand the extent of the compromise. This includes identifying the compromised data, tracking the attacker’s actions, and implementing measures to prevent future breaches.
How to Do iCloud Forensics Effectively?
When it comes to extracting the evidence from iCloud and analyzing the same effectively, there is no option better than the professional forensic analysis tool (mentioned earlier). This tool is famous among law enforcement and digital forensics professionals.
This is a specialized tool designed to perform email forensics investigation, hosted server and cloud-based storage investigation, and investigation of images and messengers. Using the advanced features of the tool, one can perform word-cloud analysis, link analysis, keyword search, and many more.
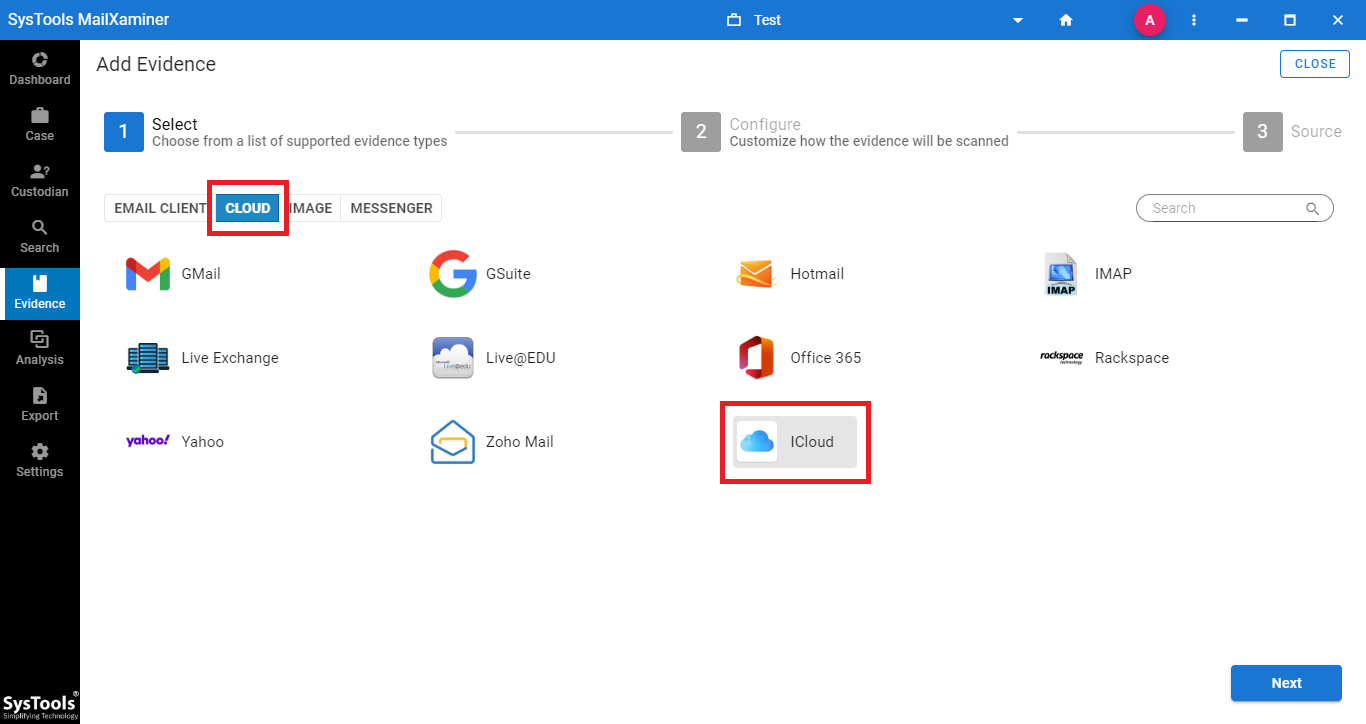
Here is the screenshot of the tool performing forensic analysis of iCloud.
Conclusion
iCloud forensics is part of a digital investigation where Apple cloud storage is involved. In this write-up, we explained what it means, what challenges forensic experts face during an investigation, different roles, and most importantly introduced a professional tool using which one can effectively perform the forensic analysis of iCloud.