Technology | 6 Minutes Reading
Email Forensic Investigation Techniques – Extract Crucial Data in The Right Way
Think of an investigator opening an inbox that contains thousands of emails. Inside those messages lies a piece of evidence that can expose fraud, insider threat, or cybercrime. Important clues remain hidden in technical details like email headers, routing paths, timestamps, and attachments. Without an efficient email forensic investigation, investigators may miss important evidence.
When an email is involved in a criminal court case, extracting the digital evidence in a court-admissible format becomes crucial. So, it would be easier for forensic investigators to carve out the evidence if they knew various techniques.
But what’s email forensics in the first place? Let’s understand this before moving ahead with the investigation techniques.
Email Forensics- Brief Introduction
The term email forensics is precisely what it sounds like. It’s a process where a digital forensic investigator analyzes emails and their content to determine the authenticity of the source, who’s the actual sender, at what time & date the message is received, etc.
In email forensics, the professionals investigate multiple aspects such as message IDs, transmission routes, attached documents & files, IP addresses of servers & computers, etc in a forensically sound manner.
The main goal of email forensics is to extract digital evidence that can be admissible in civil or criminal court. And, the investigator must know different email forensic investigation techniques to do the same.
So without further ado, let’s dig deeper and discuss the investigation practices in detail.
Various Email Forensic Investigation Techniques To Examine Emails
Sending/receiving an email seems like a very easy process. But, there are a lot more technicalities involved in this process than you think. Hence, when an email is put under investigation, various approaches are applied to carve out the exact evidence. These approaches are as follows.
Email Header Forensics
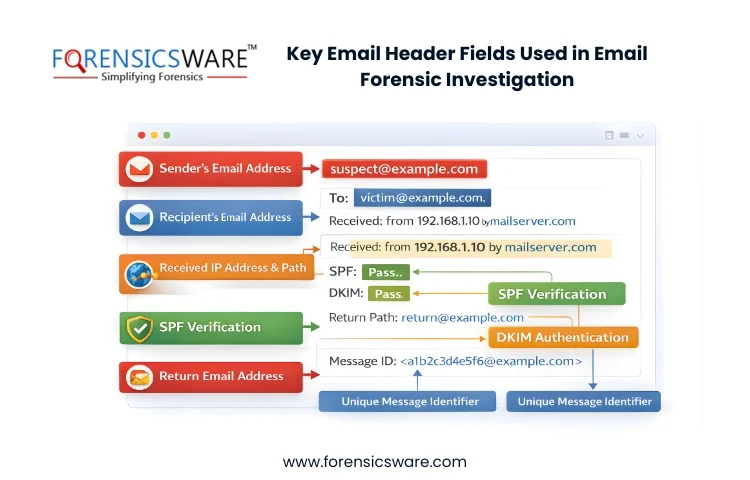
The email header is the first aspect that the investigator examines. It contains essential information such as the names of the sender & receiver and the path through which the message has been transmitted, the date & time the message received, etc. It also comprises other crucial information about SPF, DKIM signature, etc.
Apart from that, the email header contains the ‘Received: From’ field through which investigators can identify the sender’s IP address & hostname. That can help collect crucial evidence and further lead them to the culprit.
Investigation of Email Servers
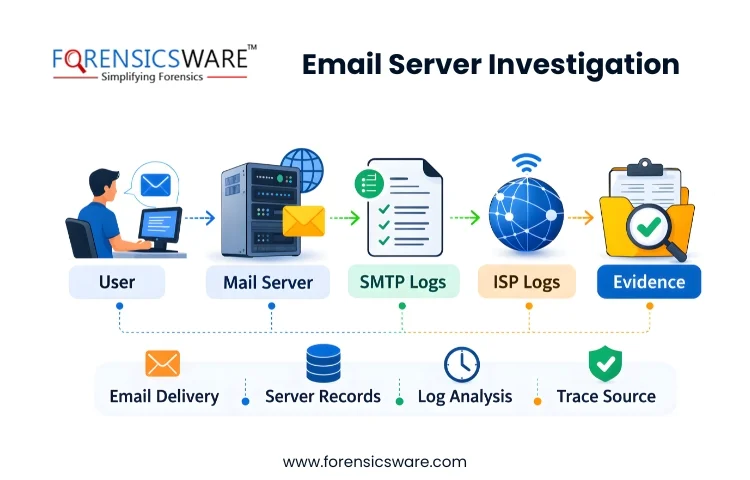
Servers maintain logs of computers’ addresses and related ISP or Proxy servers usually save copies of emails after delivery. So, an email forensic investigation involving investigating email servers would be helpful to locate the source of the email. For instance, if an email is deleted from a client’s application, sender’s, or receiver’s then it can be easily traced through proxy servers.
Also, Internet Service Providers (ISPs) frequently archive Hypertext Transfer Protocol (HTTP) and Simple Mail Transfer Protocol (SMTP) logs. Since a log is archived, it’s better to examine them as soon as possible to save time and effort in extracting & tracing relevant emails.
Network Device Investigation
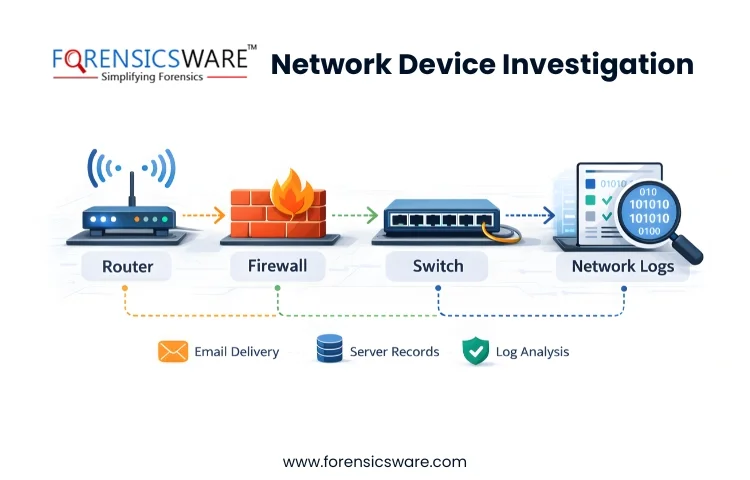
Sometimes servers are not configured to maintain logs and the ISPs refuse to share the log files. In these scenarios, email forensic investigation of servers won’t be helpful. Thus, to find evidence, email forensic professionals can turn to log files maintained by network devices such as switches, firewalls, and routers to trace the source of the email.
Software Embedded Analysis
At times, the email software used by the sender includes additional information about the email and its attached files. Interestingly, that information can be found in Multipurpose Internet Mail Extension (MIME) as a custom header.
A deep analysis of the above fields can help investigators find crucial information. This email forensic investigation technique can disclose information related to the sender such as the MAC address, Windows login username of the sender, PST file name, and many more details.
Analysis of Sender Mail Fingerprints
Oftentimes, X-headers are added to the standard headers for spam filter information, authentication results, etc. It can come in handy in finding the software handling the email client, such as Outlook or Opera Mail. And, sometimes helps identify the IP address of the sender.
Examining Volatile Memory
Recent research shows that evidence of email spoofing has been extracted from the volatile memory of the target machine. Since everything passes through volatile memory, examining the same could reveal email-related evidence.
Attachment Analysis

Most of the time email frauds are being done through email attachments. Malicious links are sent through attachments to collect the sensitive information of the victim. So, analyzing email attachments is also a critical part of the investigation.
Practice of Using Hash Values
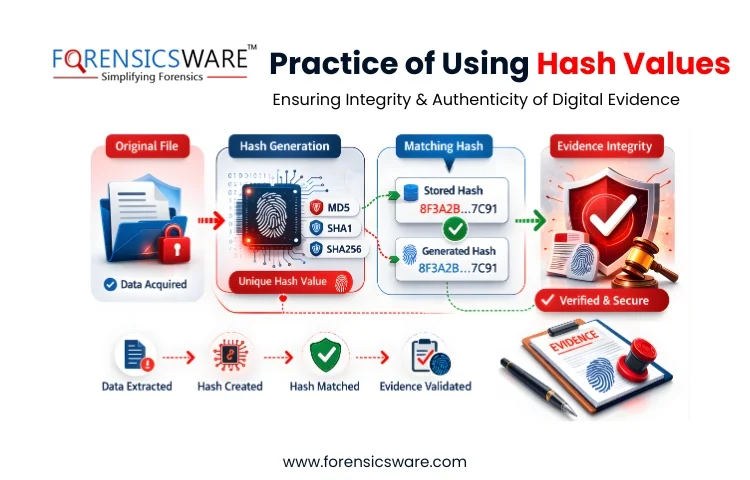
Hash values or hashing algorithms such as MD5 and SHA-1 play a crucial role in email forensic investigation. These values help forensic professionals to preserve digital evidence the moment it’s acquired. Hash values act as an added benefit when the electronic proof is shared with legal professionals.
Investigation With the Help of a Professional Tool
Email forensic investigation can be a complex task if you don’t have the right support in the form of a tool and/or professional. The forensic investigation could involve many suspects and a large number of emails to examine.
Hence, seeking help from professionals who are certified forensic investigators would be beneficial. Cause they will use the modern and advanced tool, MailXaminer to investigate the emails. With the loaded features such as different view options, ultimate keyword search filter, bulk email analysis, etc, the investigation process will yield accurate results.
Last but not least, the report generated at the end of the investigation process proved to be helpful in sharing with the legal professionals. Thus, using a professional tool for investigation has eventually become one of the best email forensic investigation techniques of all.
Frequently Asked Questions
Q. Why is email forensic investigation necessary?
It is vital to uncover and analyze the digital evidence related to email communication. This process can be beneficial in legal proceedings.
Q. What type of cases require forensic investigation of emails?
Mainly, the cases involving cyber fraud, intellectual property theft, and other cases involving emails require a proper investigation to find the culprit.
Q. What information can be extracted by doing an email investigation?
Information about sender and recipient addresses, timestamps, server information, routing details, etc.
Q. Can deleted emails be recovered in an email forensic investigation?
Yes. When you use professional tools for the investigation, you will likely be able to recover deleted emails.
Q. How is email investigation used in cyber forensics?
An email investigation in cyber forensics involves the analysis of email headers, attachments, and server logs to trace the origin of suspicious emails. The main aim of email investigation is to collect digital evidence through emails for cybersecurity or legal investigations.