Technology | 5 Minutes Reading
Email Spoofing, Inspection, and Protection Against It!

Email Spoofing is a deceptive attempt where changes in the sender’s address and other header components are done to misinterpret the origin of the message. This technique is generally adopted by spammers as an attempt to make a message being opened by the recipient or even respond to it with the intention of information theft. For example: Emails appear to have come from a legitimate institution like a bank asking to log in to an account.
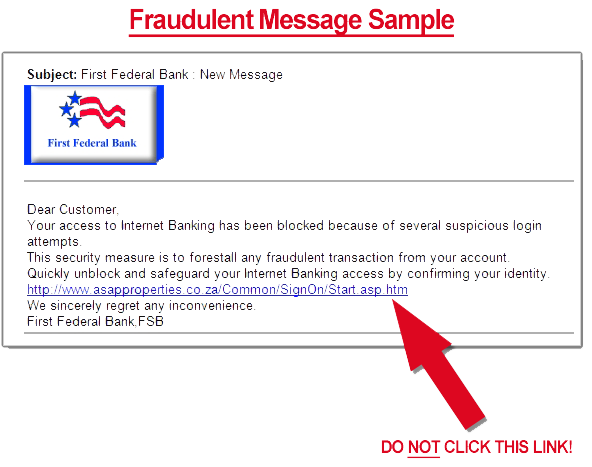
You will know your email has been spoofed when you receive a fake email (spoofed email) from the spammer. It might contain a link to a spoofed website, for example, an online banking service. The false website appears to be similar to the original one and prompts for account login details (the username and password). When you enter the information, an error like “Website is Unavailable” will be reverted and during this course of time, the spammer will dishonestly steal the confidential information for illegal profits.
Why Email Spoofing is Easy for Spammers?
“An email over the internet is easy to spoof and trusting it without any strong security enhancements like Digital Signature is not a good idea. For example: An email exchanged over internet hosts uses a protocol that is a combination of simple ASCII character commands.
Using Telnet, these commands can help to connect with SMTP port of the system. This way, the receiving host trusts the sending host and the hacker easily changes its original address to a targeted address!”
How to Inspect a Spoofed Email?
Fake email reflects a particular behavior that normal messages don’t. Here are some of the ways that can help to identify if an email is legitimate or if it is an address spoofing by spammers:
- Check the Link in the Mails: If an email contains a link to another website, just hover your mouse over the link and you will see the destination where the link would be directed to. If it is to a legitimate site, it would be a normal link like “https://amazon.com” but if it is a spoofed website, it will seem like “slp.clickr***#apsr###sin::us”. Also, if a site is prompting you for confidential details, check out an HTTP connection with SSL which can be verified with a lock icon before “https” in the link.
- Any Threat or Request: If the spam email has requested to provide account login information or uses any threatening words like “failure to which your account will be permanently deactivated”, it is a sign that the message has come from an illegitimate site. Plus, it is important to know that a message that has come from institutions like banks, credit cards, and PayPal does not confirm account details through email.
- Language and Attachments: If the language used in email spoofing seems to be too good to be true or has spelling mistakes, it means something is fishy. Messages with texts like “You won a Lottery”, and “Win by Clicking here” are quite abnormal. Plus, attachments in the file (especially .exe, .zip, .bat) have high risk.
- Missing Logo or Image in the Body: If the email appears to have arrived from a commercial, educational, or financial institute, notice if the company’s logo is there in the mail. Also, if the body of the fake email is a combination of images and text, then beware! Adding links to images is the most common fraudulent technique used by spammers.
Above are the ways of inspecting spoofed email in general. However, if you’re a professional forensics investigator and want to inspect and analyze email headers, attachments, hash values, etc in one place then try MailXaminer. It is the one-stop solution to track email spoofing incidents.
Measures to Address Spoofing
Over time, several methods have been developed to detect or track a spoofed email. SPF, DKIM, Sender ID, and DMARC are a few of them.
Sender Framework Policy (SPF) is an anti-spam technique where a fake email is identified against forging (changes in header components). Nowadays, most of the abusive messages use a fake sender address. This not only diminishes the reputation of the victim whose address is used as the sender but also wastes his time from getting the IP from the blacklist.
SPF in an internet header gives a hint about the spam email forgery on its way to the target mailbox while traversing different MTAs. SPF for a domain helps administrators define which hosts can send mail through it by creating SPF records in the Domain Name System. When an email is exchanged between two hosts, the SPF checks out if the message is being sent by a host sanctioned under the domain.
Frequently Asked Questions Related to Email Spoofing
Q- What is the purpose of spoofing email?
The main aim is to conduct phishing attacks, spread malware, or trick recipients into revealing sensitive information.
Q- How to spot a spoofed email?
There are many signs that you can notice. Such as mismatched sender addresses, unexpected email content, a sense of urgency in the email asking for your login credentials, or suspicious links.
Q- Can organizations protect themselves against email spoofing?
Yes. They can take the help of tools such as SPF or opt for professional employee training on recognizing spoofed emails.


